
What is a Risk Assessment? – Learn The 5 Steps to a Risk Assessment
What is the Purpose of a Risk Assessment?
Most information security frameworks require a formally documented, annual risk assessment. You will see this requirement over and over again in your pursuit of SOC 1, SOC 2, PCI DSS, HIPAA, or HITRUST CSF compliance. But what exactly is a risk assessment and why is it so important to information security frameworks? Let’s find out.
What is a Risk Assessment?
A risk assessment is a methodology used to identify, assess, and prioritize organizational risk. Without a risk assessment, organizations can be left unaware of where their critical assets live and what the risks to those assets are. Risk assessments evaluate the likelihood and impact of those threats actually happening and give you an opportunity to evaluate your current security controls to determine if what you’re doing will be an effective defense mechanism against a malicious attack.
One way to look at a formal risk assessment process is that your organization is now being proactive rather than reactive. If you have the opportunity to anticipate a potential security incident and address the potential adverse impacts, chances are you will be successful and save your business from any operational and reputational loss.
In relation to a SOC 1 audit, the controls that you select to be tested and described in your SOC 1 report need to be based off of your risk assessment. You must determine what risks you’re facing in the achievement of your control objectives and then you must implement the controls in order to address that risk.
5 Steps to a Risk Assessment
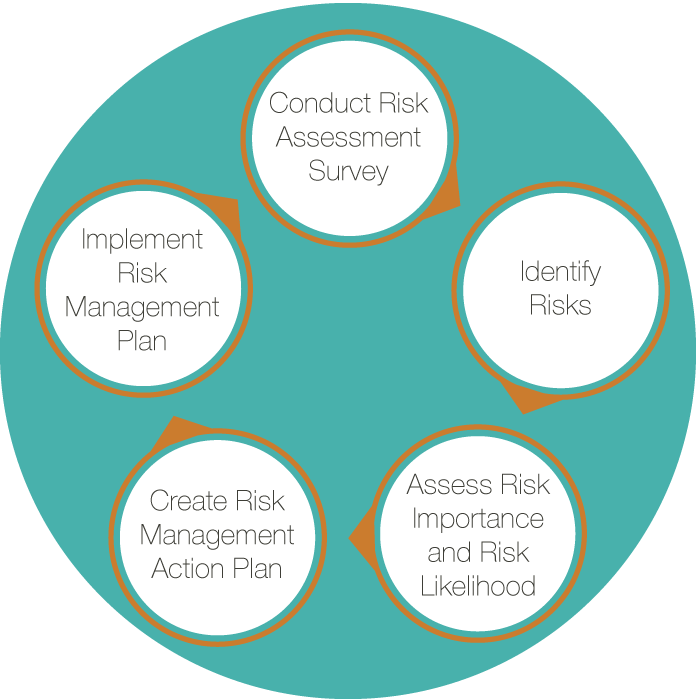
A risk assessment is a systematic process of evaluating existing controls and assessing their adequacy against the potential operational, reputational, and compliance threats identified in a risk analysis. The risk assessment process must be a continual, monitored process to be effective. So, where do you begin? The five steps to a risk assessment include:
- Conduct Risk Assessment Survey – Input from management and department heads is vital to the risk assessment process. This survey is an avenue to document specific risks or threats within a department.
- Identify Risks – The purpose of a risk assessment is to evaluate something like an IT system and ask, what are the risks to hardware, software, data, and IT personnel? What are the potential adverse events, like fire, human error, bomb threats, or flooding? What’s the potential for a loss of integrity, availability, or confidentiality in your systems?
- Assess Risk Importance and Risk Likelihood – What is the likelihood of a specific event having a negative impact on an asset? This can be expressed subjectively or quantitatively (High, Medium, Low or 1, 2, 3).
- Create a Risk Management Action Plan – Based on your analysis of which assets are valuable and which threats are likely to negatively affect those assets, you must develop control recommendations to either mitigate, transfer, accept, or avoid the risk.
- Implement a Risk Management Plan – Now that you’ve completed the first four steps to a risk assessment, you’ve developed an effective way to identify and manage risk. Now, it’s time to train your team and implement these controls.
Want to learn more about how KirkpatrickPrice’s risk assessment services can help secure your business? Contact us today.
More Risk Assessment Resources
Risk Assessment Guide and Matrix
Vendor Compliance Management Series: Performing an Effective Risk Assessment
Information Security Management Series: Risk Assessment
CFPB Readiness Series: Making Risk Assessment Work For You
A risk assessment is an important component of an SSAE 18 (recently updated from SSAE 16) because the controls that you select to describe in your report and that the auditor will test must be based on that assessment of risk. You must determine what risks you’re facing in the achievement of your control objectives and then you must implement the controls in order to address those risk. We get these questions all the time – What is the purpose of a risk assessment? What are the steps to a risk assessment?What should go into a report? What controls should we have in place? The answer to that is: What risks are you trying to address? That’s part of our process so that we can help you identify what those risks are. Understand the concept of risk assessment and why it’s so important for the SOC 1. That really and truly is the thing that determines what goes into your report.