SOC 2 Academy: Physical Security Controls
Common Criteria 6.4
During a SOC 2 audit engagement, an auditor will validate that an organization complies with the common criteria listed in the 2017 SOC 2 Trust Services Criteria, which means that they will assess an organization’s compliance with common criteria 6.4. Common criteria 6.4 says, “The entity restricts physical access to facilities and protected information assets (for example, data center facilities, backup media storage, and other sensitive locations) to authorized personnel to meet the entity’s objectives.” How can organizations comply with this requirement? What kind of physical security controls should organizations implement?
Implementing Physical Security Controls
While malicious hackers often attack digitally, organizations must account for the risk that their physical environments could be compromised too. This means that implementing physical security controls in facilities or other locations that hold sensitive information needs to be a top priority for organizations. For example, if an organization distributes access cards to all employees, how are those access cards managed? Can you clearly identify who the access card belongs to? Is there a process in place for validating that the person using the card is the same person it belongs to? What processes are in place to revoke a card if an employee is terminated or quits? Social engineering is a serious threat to many organizations, but it’s often a thought that gets put on the back burner. If you’re pursuing SOC 2 compliance, consider implementing these physical security controls:
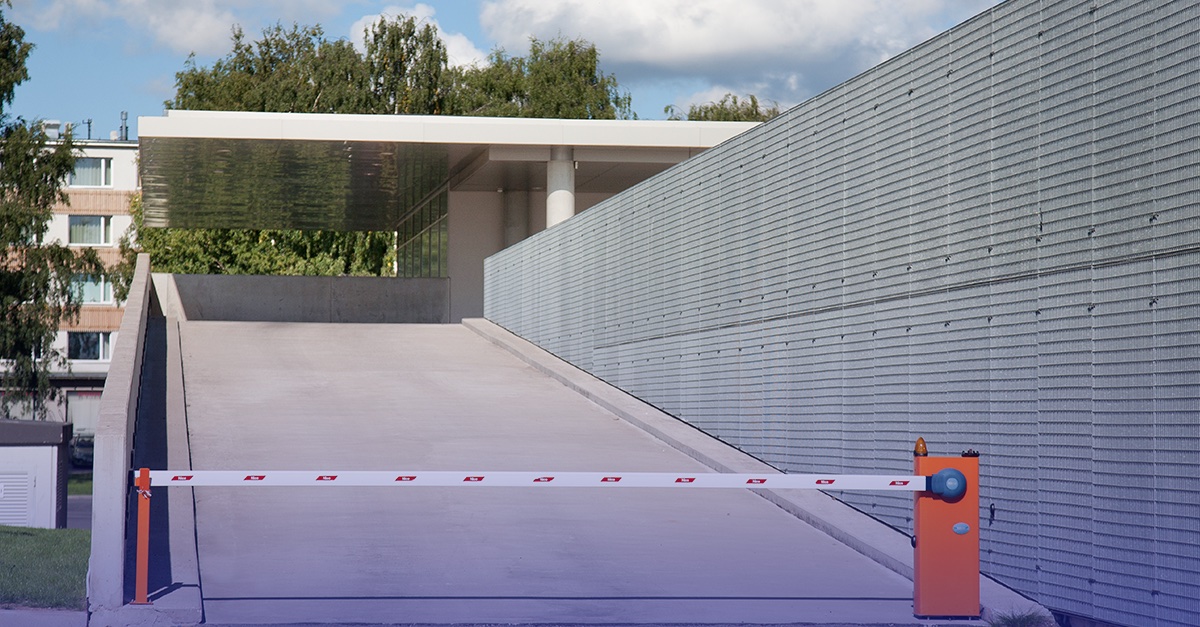
- Locks, fences, or gates
- Surveillance cameras
- Access cards
- Biometric access controls
- Security guards
Physical Security and SOC 2 Compliance
We often have clients ask us if an onsite visit is necessary when undergoing an audit, and it absolutely is. Why? Because it’s essential for assessing an organization’s compliance with common criteria 6.4. How would an auditor be able to verify that your physical security controls are in place and working efficiently without physically testing them? During a SOC 2 audit, an auditor will physically need to validate that the physical security controls that you say are in place are actually working as intended.
More SOC 2 Resources
Understanding Your SOC 2 Report
SOC 2 Compliance Handbook: The 5 Trust Services Criteria
Common criteria 6.4 in the 2017 SOC 2 Trust Services Criteria deals with physical security. Let’s say that you have an access control card system. One of the things that we recommend is that you do your own internal audit of the cards that you have versus that cards that are active in the system. You need to make sure that any lost cards get deactivated and that you, in a very timely manner, remove employees or vendors who have been issued cards and are no longer employed by the organization. This is so there aren’t unauthorized people still in the system and the system is current. You also want to think about where all of the areas are where you need to have physical security controls. Too often, people think that just because they work in a corporate office, they shouldn’t care about physical security controls. However, the corporate office still has all the critical people who use their systems to log in to things such as production networks at a data center or resources in the cloud. You still wouldn’t want your physical security, even in an administrative area, to be compromised because someone might access a laptop, steal a piece of media, or gain access to paper records that are laying around. We have that happen a lot where clients say, “There’s nothing here that we’re trying to protect. Everything we have is in the cloud.” Yet, when you do a little bit of digging, we find that there are some hard copy materials, removable media, and clearly, systems that can be used to access the information in the cloud. You need to think about physical security controls, where they should be applied, and make sure that you find the best way to implement locks, card readers, and any other type of physical control that’s appropriate for your situation.