
Episode 1 – Who is HITRUST & What is the HITRUST CSF?
Have you been asked by a top client to become HITRUST CSF certified? Are you looking for a better way to demonstrate compliance with HIPAA laws? What exactly is HITRUST and how does it apply to your organization? KirkpatrickPrice is an approved HITRUST CSF Assessor, prepared to help Business Associates understand who HITRUST is, what the HITRUST CSF is, and how you can apply HITRUST CSF certification to your organization.
Who is HITRUST?
HITRUST Alliance is an independent, not-for-profit organization, was established in 2007 and was “born out of the belief that information protection should be a core pillar of, rather than an obstacle to, the broad adoption of health information systems and exchanges.” Over the last several years, the HITRUST CSF certification has really begun to gain momentum as Covered Entities are regularly adopting the HITRUST CSF framework. 80% of hospitals, insurance carriers, and health plans have or are adopting the HITRUST CSF framework, and it has become the most widely used framework across the healthcare industry. HITRUST Alliance’s Board of Directors is made up of experienced individuals from organizations like Anthem, Walgreens, and UnitedHealth Group. HITRUST updates the HITRUST CSF on an annual basis, paying special attention to the current and evolving threat landscape and breach data while collaborating with regulators to create a comprehensive framework that provides a road map for demonstrating due diligence for maintaining HIPAA compliance.
What is the HITRUST CSF?
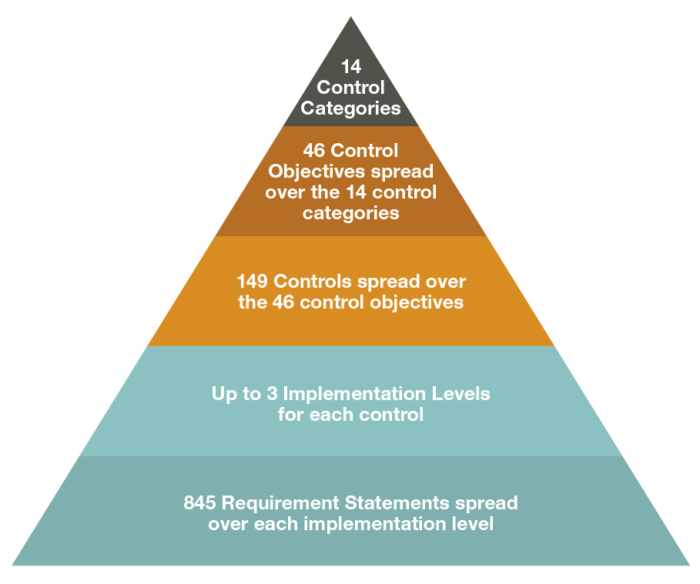
The HITRUST Common Security Framework, or CSF, is a security and privacy framework, the basis of what HITRUST has developed and maintains for the healthcare industry. The hierarchy of the framework is constructed similarly to ISO 27001/27001 and consists of 14 control categories which contain 46 control objectives that map to 149 controls. Within each of the 149 controls, there are up to 3 implementation levels in which you must meet for each risk factor involved. Risk factors include organizational, system, and regulatory. In all, there are 845 requirement statements spread over each implementation level.
It’s important to remember that the HITRUST CSF is very scalable, thus the basis of its appeal. Depending on the size of your organization, the number of records you’re maintaining, and whether you’ve scoped your environment effectively, not all 845 requirements will apply to your organization. In the following HITRUST videos, we will dive in to a more granular level and explore what applies to you, how it applies to you, and how you can begin your HITRUST CSF certification journey.
Why HITRUST CSF Certification?
You may be asking yourself, “Why do I need this? Why is my client asking me for yet another framework?” If you’re managing healthcare data, it’s critical from a business and reputational standpoint to protect yourself from risk and maintain a strong relationship with your clients who are also trying to mitigate their risks. HITRUST certification is a great way to ensure this is happening.
HITRUST certification is also a great way to demonstrate compliance with HIPAA laws. The HITRUST CSF certification demonstrates a high level of due diligence that you are doing everything you possibly can to protect the healthcare data for which you are responsible. HIPAA has been around since 1996, however, it only provides basic guidelines for organizations to follow and doesn’t go in to detail on how to maintain the controls. The HITRUST CSF is effective because not only is it scalable based on your unique risks, but it also provides guidance on how to meet specific controls.
Because the HITRUST CSF was built on the ISO 27001/27002 framework and incorporates elements of other frameworks such as PCI DSS, NIST 800-53, and COBIT, it aligns itself nicely with other frameworks your clients are likely asking you about. Since there is a lot of crossover, this can increase efficiency and decrease costs for your organization. The HITRUST CSF is certifiable and attractive to Covered Entities because they know what HITRUST is and see it as a great way to measure, mitigate, and control risks at your organization. Contact me today at s.morris@3.95.165.71 for help with establishing a relationship with HITRUST and get started with your HITRUST compliance journey today.
Hi, I’m Jessie Skibbe! I’m the Vice President of Strategic Development and Chief Compliance Officer for KirkpatrickPrice. Thanks for joining me today! We want to take you on a journey to describe what HITRUST compliance really means, starting off with: Who is HITRUST? What is the CSF? How do I apply it to my organization? First, just a little bit about me. I have been in the role of Information Security Officer, Network Administrator, and Chief Compliance Officer, spanning my career of 25 years in manufacturing, financial services, and healthcare industries. In my current role, my primary objective is to help our clients achieve their security and compliance objectives. Many of our clients – being the Business Associate in a lot of cases – really have a multiple-audit challenge that they have to deal with.
A little bit about our firm: we have been practicing for over 12 years. We are a licensed CPA firm as well as a PCI QSA firm and, of course, a HITRUST Assessor firm. We have a wide variety of services to offer to help you meet your compliance objectives. I’m going to start with giving you a background of who HITRUST is – not to be confused with the HITECH Act or HIPAA. HITRUST is an independent organization. They are a not-for-profit organization. They were established in 2007, so they’ve just celebrated their 10-year anniversary. Most recently, over the last 3 years, they’ve gained a lot of momentum with Covered Entities, hospitals, and payers really adopting their framework. A statistic I read on their website recently showed that 80% of hospitals and payers have both adopted the framework, making it the most widely-used framework across the healthcare industry. HITRUST themselves, like I mentioned, is an independent organization. The Board of Directors behind HITRUST is from companies such as Anthem, United Health Group, and Walgreens, just to name a few. You can go to their website, that we’re going to show you here on-screen, that will take you to the “About Us,” obviously, shows you who the Board of Directors are, which is made up of healthcare industry professionals that are really guiding and directing the initiative of HITRUST.
HITRUST is updating the CSF framework every year. The important thing about that, and what can really make you feel good about adopting the framework, is that they’re paying attention to the cyber threat and intelligence that’s happening in the industry right now, they’re paying attention to breach data, and they’re working closely with regulators to create a comprehensive framework that will self-regulate and provide due diligence with maintain HIPAA compliance, specifically, across the healthcare industry. It’s something that you can feel good about implementing. Whether this is something that your client says you have to do, or whether it’s something that you’re choosing on your own accord to do for a great level of due diligence, HITRUST has committed to their users and people who’ve adopted the framework that they will continue to update it year after year after year. So that’s a little bit about who HITRUST is.
Now let’s talk about what the CSF is. So, what is the CSF? The CSF, as I described, is the Common Security Framework. It’s the core of what HITRUST maintains for the healthcare industry. I’m going to give you a lot of numbers to really describe what the CSF is. What’s it’s important to note – I described earlier how it’s widely adopted – 23,000 CSF assessments have been performed in the last few years, 10,000 of those in 2014. There’s been a push in the last 2-3 years of the number of assessments being performed. Like I mentioned, I’m going to give you a lot of numbers to describe the CSF, those being a few. To understand how the hierarchy works and how the CSF is constructed, it follows ISO 27001/27002 very closely. There are 14 control categories, containing 46 control objectives mapping to 149 controls. Within each of those 149 controls, there’s also up to 3 levels of implementation requirements that you have to meet based on the risk factors involved, which are organizational, system, and regulatory risk factors, which I’m going to explain a whole lot more in the next video when we talk about how to use the CSF to apply it to your organization. That, from a high-level, is how the CSF is constructed. Important to note, too – there are up to 845 requirement statements that you must be compliant with. Those are individual tests that must be performed when you’re going through the evaluation. The good news is, I hope that number doesn’t scare you off, because the HITRUST CSF is very scalable depending on the size of your organization, the number of records you’re maintaining, and the system that you have scoped out effectively. Not all of those 845 requirement statements are going to apply to you. My objective for this series of videos is to walk you through how to determine what applies to you, what doesn’t apply to you, and how you can begin your path in maintaining HITRUST compliance.
So, I described from a 10,000-foot level what the Common Security Framework is, but I want to give you some piece of mind because you may be wondering: why do I need this? Why is my client asking me to be compliant with 1 more framework? Why should you have to go through all of this trouble? If you’re maintaining healthcare data, it’s really important for you from a business standpoint and protecting yourself from risk, as well as maintaining that strong relationship with your client that’s trying to mitigate their risks. If you’re not sure what risks apply to you, then I would highly suggest a visit to the HHS Newsroom. Most recently, I read about a $5 million resolution agreement with a hospital system. It’s not only affecting Covered Entities; there are OCR resolution agreements going into place with Business Associates. That’s one reason, obviously the OCR is really gaining momentum with the audits and the resolution agreements that they’re putting into place now for companies that are not maintaining compliance with HIPAA. But also from a financial perspective, thinking about potentially providing breach notification to all those consumers that you have in your database. Protecting yourself from a data breach is the right thing to do from a business standpoint, from a reputational risk standpoint, and to maintain that strong relationship with your client. The Covered Entity, hospital, or network, depending on what you’re doing for them as a Business Associate, it’s necessary to show them and demonstrate to them that you are doing the right things, doing due diligence, and maintaining compliance with HIPAA. The CSF wraps itself beautifully around the HIPAA Security Rule. There are elements of Privacy that I’ll talk a little bit about later, but it’s primarily the Security Rule. If for no other reason, go to that HSS Newsroom and read about some of the risks that apply to you as a Business Associate as well as a Covered Entity, as far as your responsibility of maintaining protection over that data. Following something like the HITRUST CSF demonstrates a high level of due diligence, that you’re doing everything that you can to protect that healthcare-related data that you’re being held responsible for keeping secure.
We all know that HIPAA has been around for a very long time, since 1986, and then in 2009 the HITECH Act really brought some enforcement to that, as well as to Business Associates. HIPAA provides a basic guideline for entities to follow, but it doesn’t get into that granularity, as far as how to necessarily maintain some of those controls. The one thing that HITRUST does very effectively, like I said, is it’s very scalable depending on what your inherent risk factors are. If you’re in areas of greater risk, you have to have greater levels of control. It’s very scalable, from that aspect, to adopt to your organization, depending on if you’re on the larger or smaller side.
We’ve displayed a graphic here for you, to demonstrate some of the other frameworks that are included in the HITRUST framework. As you’ll see at the core, it’s built on ISO 27001/27002 standard, that being the international standard for information security and maintaining a management system that incorporates a risk management framework. This fits nicely with the scalability of the HITRUST CSF framework. Built on ISO, incorporating elements from PCI; as you’ll see, not all of PCI is covered, but we’re estimating that about 80% of PCI is covered within the framework. You’ll also see NIST 800-53, as well as a portion of COBIT. The one nice thing about the CSF is that it helps you gain efficiency within your compliance efforts if you have clients that are asking you for a lot of different types of compliance. If they’re asking you to be compliant with NIST, for example, if you’re doing any work and have to be compliant with FISMA. If you’re, for example, also a vendor to someone and you’re collecting credit card information or processing credit card information yourself, you’ll know that that crossover between the CSF and PCI exists. The HITRUST CSF framework can increase efficiency and reduce cost for your organization. That’s another reason why the framework was developed. So, as I was saying, the HITRUST CSF framework really aligns itself nicely with other frameworks that you may already have to be compliant with. One thing I’d really like to stress is that it’s a certifiable framework, which makes it really nice and attractive from a Covered Entities standpoint. You can achieve “HITRUST Certified” and they know what that means. They know the scalability, they know the Requirement Statements, they know the Controls that are requested in the CSF. It’s a really good way to control and mitigate risk from the Covered Entities standpoint.
In our next video, I’m really going to drill down with you. Like I mentioned, there 845 requirement statements. In our next video, I’m going to take you through how to determine what the scope of your environment is, and then how to apply that scope to navigate the CSF and how to apply those controls to your environment. Thank you so much for joining us today! We hope it was a valuable use of your time and we definitely hope to see you in the next video. As always, you can contact us immediately at the information below. We hope to be your trusted partner in meeting your compliance objectives.