What is a Point of Focus?
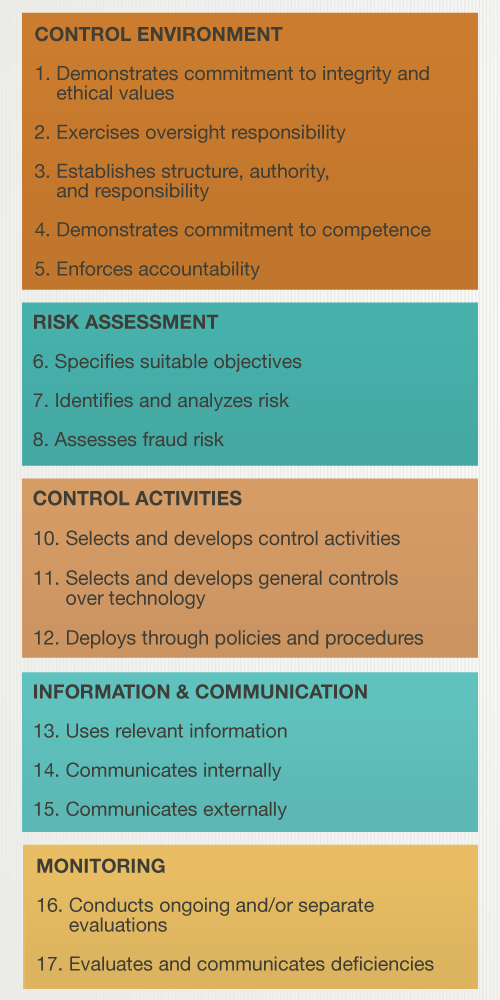
In the past, many organizations have struggled on their journey toward SOC 2 compliance because they lacked an understanding of what they needed to do to comply with the Trust Services Criteria. As such, one of the enhancements to SOC 2 reporting includes points of focus, which will assist organizations when they are designing, implementing, operating, and evaluating controls over security, availability, confidentiality, processing integrity, and privacy. Points of focus are meant to be references, not requirements because not all points of focus will be applicable to all organizations. These points of focus serve as a type of checklist for management, providing clarity on how organizations can ensure that they are SOC 2 compliant. Let’s look at an example of points of focus under the security category.
Specific Points of Focus
For example, CC1.1, under the common criteria and COSO’s control environment component, states, “The entity demonstrates a commitment to integrity and ethical values.” The specific points of focus for this include the following:
- Sets the Tone at the Top—The board of directors and management, at all levels, demonstrate through their directives, actions, and behavior the importance of integrity and ethical values to support the functioning of the system of internal control.
- Establishes Standards of Conduct—The expectations of the board of directors and senior management concerning integrity and ethical values are defined in the entity’s standards of conduct and understood at all levels of the entity and by outsourced service providers and business partners.
- Evaluates Adherence to Standards of Conduct—Processes are in place to evaluate the performance of individuals and teams against the entity’s expected standards of conduct.
- Addresses Deviations in a Timely Manner—Deviations from the entity’s expected standards of conduct are identified and remedied in a timely and consistent manner.
- Considers Contractors and Vendor Employees in Demonstrating Its Commitment – Management and the board of directors consider the use of contractors and vendor employees in its processes for establishing standards of conduct, evaluating adherence to those standards, and addressing deviations in a timely manner.
Organizations pursuing SOC 2 compliance would then choose to follow the guidance of the points of focus that apply to them. This ensures that their controls demonstrate the organization’s commitment to integrity and ethical values.
More SOC 2 Resources
Understanding Your SOC 2 Report
SOC 2 Compliance Handbook: The 5 Trust Services Criteria
[av_toggle_container initial=’1′ mode=’accordion’ sort=” styling=” colors=” font_color=” background_color=” border_color=” custom_class=”]
[av_toggle title=’Video Transcript’ tags=”]
One of the enhancements to the SOC 2 Trust Services Criteria in 2017 has to do with the inclusion of points of focus. The criteria now include points of focus, given by the AICPA, that really give you important characteristics about the criteria. These are not requirements; these are not things that you have to do, but they’re very helpful to reference. You can go into our Online Audit Manager and check out the resources in order to find these points of focus. One of the things that’s been very helpful about it is, many times in the SOC 2 criteria, you would read it and you wouldn’t really understand, at first glance, what it was talking about. The points of focus are there to help you understand the context of what the criteria is seeking to accomplish and how you might implement that within your own organization.
[/av_toggle]
[/av_toggle_container]


 These myths about Business Continuity and Disaster Recovery Plans for the cloud are hurting businesses. This way of thinking couldn’t be further from the truth. Business Continuity and Disaster Recovery Plans are not simply a technology roadmap; they describe how to recover business operations, which includes people and processes. How could a cloud service provider determine how your people and processes will recover?
These myths about Business Continuity and Disaster Recovery Plans for the cloud are hurting businesses. This way of thinking couldn’t be further from the truth. Business Continuity and Disaster Recovery Plans are not simply a technology roadmap; they describe how to recover business operations, which includes people and processes. How could a cloud service provider determine how your people and processes will recover? Michael Burke is an Information Security Specialist with KirkpatrickPrice with over 25 years of experience in the information technology industry. Michael holds a PhD in Information Technology from Capella University. He is a member of the EC-Council, the International Information Systems Security Certification Consortium, and the Project Management Institute. Michael also holds CISSP, CCISO, QSA, and CCSFP certifications.
Michael Burke is an Information Security Specialist with KirkpatrickPrice with over 25 years of experience in the information technology industry. Michael holds a PhD in Information Technology from Capella University. He is a member of the EC-Council, the International Information Systems Security Certification Consortium, and the Project Management Institute. Michael also holds CISSP, CCISO, QSA, and CCSFP certifications.
 Internal audit provides a level of monitoring which is generally not available when working with a third-party auditor. If you’re going on a long road trip, how likely are you to hop in the car and start driving? You’re not – most people will take the car to the shop for an oil change and overall inspection. If the road trip is the audit engagement, the practice of taking the car to the shop equates to the usage of an internal audit function to ensure the car (the organization) is ready for the road trip (the third-party assessment).
Internal audit provides a level of monitoring which is generally not available when working with a third-party auditor. If you’re going on a long road trip, how likely are you to hop in the car and start driving? You’re not – most people will take the car to the shop for an oil change and overall inspection. If the road trip is the audit engagement, the practice of taking the car to the shop equates to the usage of an internal audit function to ensure the car (the organization) is ready for the road trip (the third-party assessment).