
Protecting Your AWS Cloud Infrastructure with AWS Network Firewall
AWS Network Firewall is a flexible managed firewall and intrusion detection service. It allows AWS users to control network access to resources within an AWS Virtual Private Cloud (VPC). We explored AWS Network Firewall and how it complements other AWS firewalls in What is AWS Network Firewall? In this article, we’ll dig a little deeper and show you how to deploy an AWS Network Firewall instance within a VPC hosted on your AWS cloud environment.
At a high level, the process for deploying AWS Network Firewall involves the following four steps:
- Create rule groups with networking filtering rules.
- Create a firewall policy that includes your rule groups.
- Create a firewall that uses your firewall policy.
- Configure VPC route tables so the firewall endpoint can process traffic as it moves between an internet gateway and subnets within your VPC.
The details of Step 4 differ depending on how your VPC is configured, so we’ll focus on the first three steps here.
AWS Network Firewall is a highly configurable service, and secure configuration depends on factors unique to your environment, including how your VPC, subnets, and gateways are configured. This article should not be taken as a guide to setting up a secure firewall for your AWS infrastructure.
AWS Network Firewall Prerequisites
To follow the steps outlined here, you will need an AWS VPC with the following characteristics:
- At least two subnets, one of which will be used only for the AWS Network Firewall.
- An Internet Gateway with routing configured to send incoming traffic to the other subnet, which should be configured to send outgoing traffic through the gateway.
The firewall subnet must have at least one available IP address. Amazon calls this configuration a simple single zone architecture with an internet gateway.
Configure Firewall Security Rules
The first step is to create firewall rules groups to contain your traffic filtering rules. For example, you might want to block incoming SSH traffic to your subnet. To do so, you would create a rule telling the firewall to drop SSH connections.
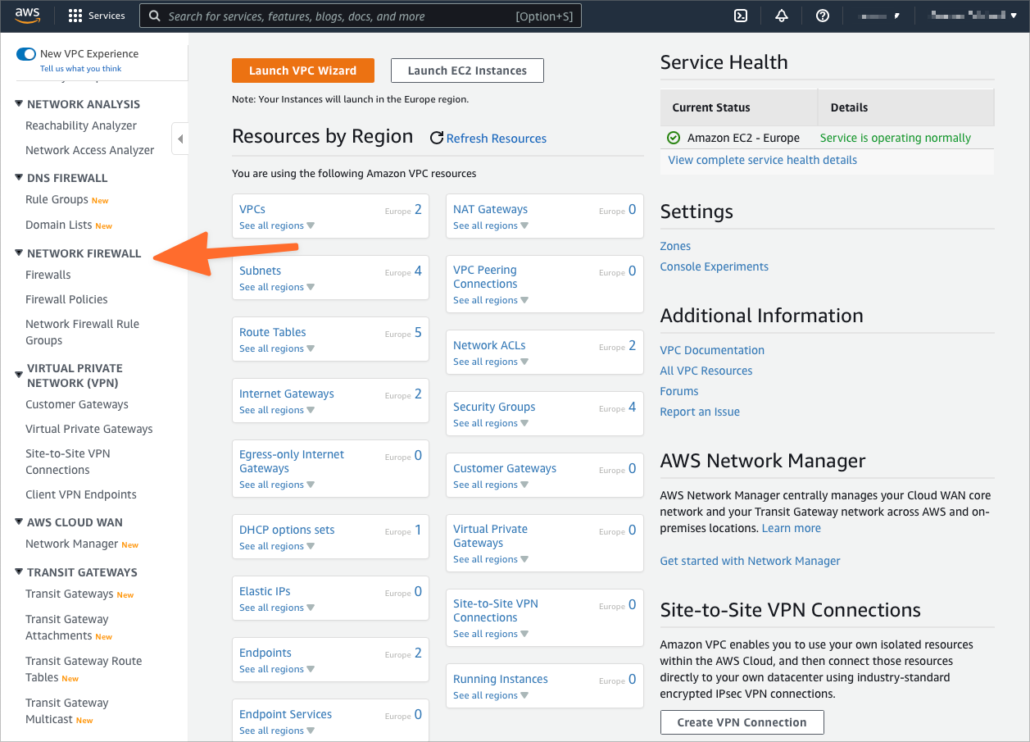
- Open the AWS VPC console and select Network Firewall Rule Groups from the Network Firewall section of the sidebar menu.
- Click the Create Network Firewall rule group button and give the group a name.
- In the Capacity field, enter a number that represents the number of rules you expect to add to this group. If you’re experimenting, 10 should be sufficient, but be aware that you cannot change this number if you want to add more rules later.
- Choose whether to create a stateless or stateful rule group.
- Scroll down to the Add Rule section and enter the new rule’s protocol, name, and source and destination IP and port.
- Choose whether packets matching the rule are dropped or passed.
- Click the Add Rule button.
- Add additional rules as required, and then click Create Stateful/Stateless Rule Group at the bottom of the page.
Learn more about how to create security rules from Amazon’s documentation.
Create a Firewall Policy
Now that you have created a rule, you can add it to a Firewall Policy.
- Select Firewall Policies from the Network Firewall section of the VPC console.
- Click the Create firewall policy button.
- Enter a name and optional description before clicking Next.
- Scroll down to the Stateless rule group or Stateful rule group forms.
- Click the Add Rules Groups button, then Add my own stateful/stateless rule groups.
- Choose the rule group you created in the previous step.
- Click through the subsequent dialogs and then click Create firewall policy on the Review and create page.
Learn more about firewall policies from Firewall policies in AWS Network Firewall.
Deploy AWS Firewall on Your Virtual Private Cloud
The next step is to create a firewall that uses the firewall policy created in the previous step. Once the firewall is configured, it will be deployed into the firewall subnet of the VPC.
- Select Firewalls from the Network Firewall section of the VPC console.
- Click the Create Firewall button.
- Give the firewall a name and choose your VPC from the drop-down menu.
- Select the availability zone that contains your firewall subnet and then the subnet itself.
- In the Associated firewall policy section, choose Associate an existing firewall policy and then choose the policy created in the previous section from the dropdown.
- At the bottom of the page, click Create Firewall.
AWS will now deploy your firewall into the chosen subnet. However, the firewall does not automatically begin filtering content. To use the firewall, you must configure the VPC’s routing tables so that incoming and outgoing traffic is sent through the firewall’s endpoints. The specifics depend on how your VPC and subnets are configured, but you can learn more about VPC routing tables in Managing route tables for your VPC.
Cloud Security and Compliance with KirkpatrickPrice
KirkpatrickPrice can help your business to secure its cloud infrastructure. Our cloud security audits and remote cloud security configuration assessments ensure your AWS infrastructure is configured for optimal security and compliance. To learn more, contact a cloud security and compliance specialist or visit our cloud security resources.