Amazon Web Services (AWS) and its peers in the cloud market have transformed infrastructure hosting for companies of all sizes. However, making the move to the cloud can be intimidating and overwhelming, and it may seem more work than it’s worth. So why has AWS cloud hosting proven to be so successful?
Having the first-mover advantage played a substantial role: Amazon entered the cloud infrastructure market before its competitors. AWS kicked off the cloud revolution two decades ago. But being first wasn’t enough—the platform’s success stems from real-world AWS benefits that help businesses to build profitable products and services.
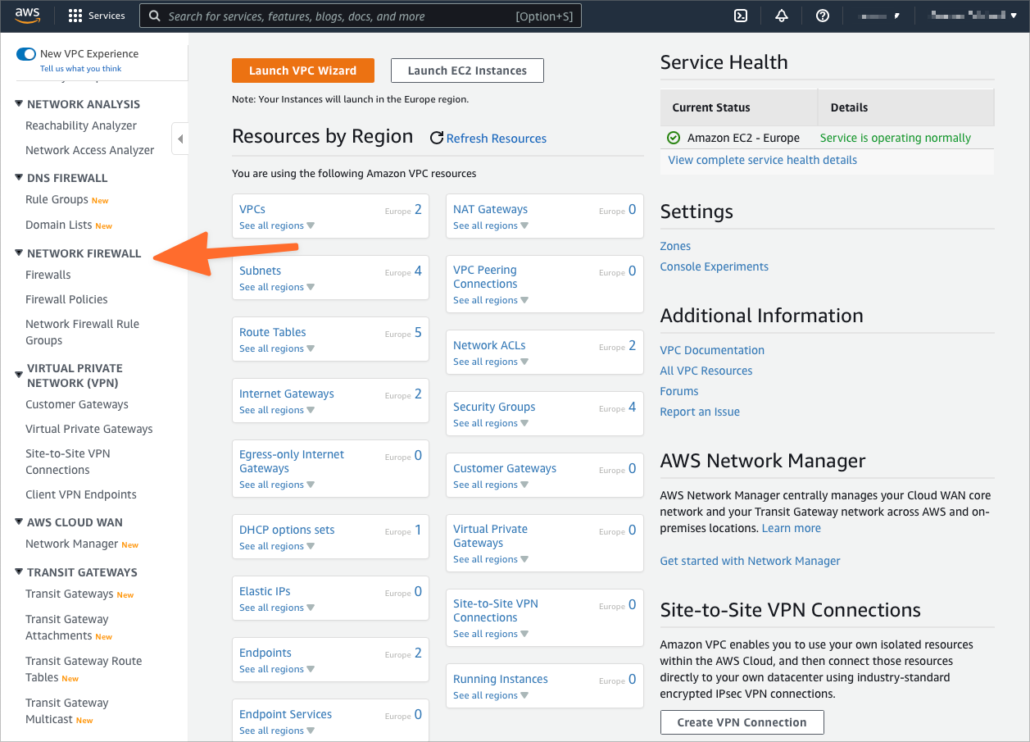
The following years saw the introduction of EC2, S3, RDS, and a host of other storage and compute services. Today, AWS offers over 100 services in domains as diverse as database hosting, virtual networking, cloud security, and machine learning. AWS is by far the biggest cloud platform globally, with a 33% market share, compared to Microsoft Azure’s 21% and Google Cloud’s 10%.
We believe AWS cloud hosting could benefit your business in 5 distinct ways. Let’s take a look at these beneficial reasons below:
1. Reduced Infrastructure Cost with On-Demand Pricing
On-demand pricing is a significant benefit of AWS and other cloud services—you pay only for the resources you use. If you need a server, you can deploy one in minutes and only pay for the compute, storage, and network resources it consumes. AWS allows users to share the underlying hardware, reducing lead times and costs compared to bought or leased IT infrastructure.
2. Scalable Compute and Storage
In the pre-cloud era, businesses bought infrastructure to accommodate peak loads, which meant they paid for resources that were idle most of the time. In contrast, the cloud’s scalability allows businesses to scale up and down as demand changes. In a well-managed cloud environment, businesses make significant savings by not paying for idle infrastructure.
3. Outsourced Infrastructure Management
Cloud platforms like AWS take care of the physical infrastructure and much of the virtual infrastructure. Cloud users are free to focus their IT resources where they generate the most value. Instead of monitoring and managing physical servers and their components, they can spin up virtual machines or take advantage of higher-level Platform-as-a-Service and Software-as-a-Service tools. Users don’t have to worry about the implementation details because they are outsourced to the cloud provider.
4. A Diverse Array of Enterprise-Grade Services
The variety of enterprise-grade services AWS provides would be extremely costly for a business to build independently. For example, AWS makes it straightforward to build highly available cloud environments with redundant infrastructure distributed across availability zones, data centers, and even continents. These redundancy and availability features are baked into the platform, and they are available to all businesses, from sole traders to giant corporations.
5. Best-in-Class AWS Security
AWS offers many services and tools to help businesses improve security and compliance. We’ve written extensively about AWS security services and best practices in previous articles, including:
- What is AWS Network Firewall?
- 10 S3 Best Practices for Improving AWS Security
- How to Achieve PCI DSS Compliance on AWS
- Best Practices for Using AWS CloudTrail
- 5 Ways AWS Security Features Strengthen Business Cloud Security and Compliance
In the early days of cloud computing, businesses worried moving to the cloud would increase security risks. They thought giving up infrastructure and software control would lead to more security vulnerabilities. In fact, the opposite is the case. Most cloud security and compliance issues are the results of cloud user error and misconfiguration.
AWS provides tools and services to help improve security, but it’s up to businesses to use them correctly. Another way of putting it is that businesses and AWS share responsibility for cloud security. The dividing line between the user’s responsibility and the platform’s responsibility is not always clear, and it can be challenging for businesses without cloud expertise to make the right decisions.
KirkpatrickPrice is here to help make sure your transition to the cloud is smooth and secure. We provide a comprehensive array of cloud security services to empower businesses to make the most of AWS while maintaining excellent security and compliance, including:
- Cloud security audits
- Remote cloud security assessments
- Compliance audits for regulations and standards that include SOC 2, SOC for Cybersecurity, PCI DSS, HIPAA, and ISO 27001.
To learn more about cloud security and compliance, check out our cloud security resources or contact a KirkpatrickPrice information security specialist.